利用openswan配置VPN服务
CentOS6.5 利用openswan xl2tpd配置VPN服务
OpenSWan是Linux下IPsec的最佳实现方式,其功能强大,最大程度地保证了数据传输中的安全性、完整性问题
OpenSWan支持2.0、2.2、2.4以及2.6内核,可以运行在不同的系统平台下,包括X86、X86_64、IA64、MIPS以及ARM
OpenSWan是开源项目FreeS/WAN停止开发后的后继分支项目,由三个主要组件构成:
配置工具(ipsec命令脚本)
Key管理工具(pluto)
内核组件(KLIPS/26sec)
26sec使用2.6内核内建模块Netkey,用来替代OpenSWan开发的KLIPS模块,2.4及以下版本内核无Netkey模块支持,只能使用KLIPS。如果你用的是2.6.9以上的内核,推荐使用26sec,可以不用给内核打Nat-T补丁就可以使用NAT,2.6.9以下版本内核的NETKEY存在Bug,推荐使用KLIPS
OpenSWan有两种连接方式:
1) Network-To-Network方式
Network-To-Network方式是把两个网络连接成一个虚拟专用网络。当连接建立后,每个子网的主机都可透明地访问远程子网的主机。要实现此种连接方式,要满足以下两个条件:
I. 每个子网各自拥有一台安装有OpenSWan的主机作为其子网的出口网关;
II.每个子网的IP段不能有叠加
2) Road Warrior方式
当使用Network-To-Network方式时,作为每个子网网关的主机不能像子网内部主机那样透明访问远程子网的主机,也就是说:
如果你是一个使用LClient的移动用户,经常出差或是在不同的地点办公,你的LClient将不能用Network-To-Network方式与公司网络进行连接。
Road Warrior方式正是为这种情况而设计的,连接建立后,你的LClient就可以连接到远程的网络了
#openswan配置
client1 192.168.10.2(网关192.168.10.1)
server1 192.168.22.210(内网192.168.10.1)
server2 192.168.22.199(内网192.168.20.1)
client2 192.168.20.2(网关192.168.20.2)
client1 ←—→ server1←———→ server2 ←—→ client2
10.2 22.210(10.1) 22.199(20.1) 20.2
安装openswan ipsec
在server:
vim /etc/sysctl.conf #开启转发
net.ipv4.ip_forward = 1
net.ipv4.conf.default.rp_filter = 0
sysctl -a | egrep "ipv4.*(accept|send)_redirects" | awk -F "=" ‘{print$1"= 0"}‘ >> /etc/sysctl.conf #禁用ICMP重定向
/sbin/sysctl -p
setenforce 0
yum install openswan lsof
# ipsec --version
Linux Openswan U2.6.32/K(no kernel code presently loaded)
See `ipsec --copyright‘ for copyright information.
# service ipsec start
ipsec_setup: Starting Openswan IPsec U2.6.32/K2.6.32-431.el6.x86_64...
# ipsec verify
Checking your system to see if IPsec got installed and started correctly:
Version check and ipsec on-path [OK]
Linux Openswan U2.6.32/K2.6.32-431.el6.x86_64 (netkey)
Checking for IPsec support in kernel [OK]
SAref kernel support [N/A]
NETKEY: Testing for disabled ICMP send_redirects [OK]
NETKEY detected, testing for disabled ICMP accept_redirects [OK]
Checking that pluto is running [OK]
Pluto listening for IKE on udp 500 [OK]
Pluto listening for NAT-T on udp 4500 [OK]
Two or more interfaces found, checking IP forwarding [OK]
Checking NAT and MASQUERADEing [OK]
Checking for ‘ip‘ command [OK]
Checking /bin/sh is not /bin/dash [OK]
Checking for ‘iptables‘ command [OK]
Opportunistic Encryption Support [DISABLED]配置ipsec
# vim /etc/ipsec.conf version 2.0 config setup protostack=netkey nat_traversal=yes virtual_private= oe=off nhelpers=0 conn net-to-net authby=secret type=tunnel ike=aes256-sha2_256;modp2048 phase2alg=aes256-sha2_256;modp2048 left=192.168.22.210 leftsubnet=192.168.10.1/24 right=192.168.22.199 rightsubnet=192.168.20.1/24 forceencaps=yes dpddelay=1 dpdtimeout=3 dpdaction=restart auto=start #sha2_truncbug=yes
# vim /etc/ipsec.d/ipsec.secrets
192.168.22.210 %any 0.0.0.0: PSK "test" #right的ip改一下
# service ipsec restart
# service ipsec status
# ipsec auto --up net-to-net #测试上面定义的net-to-net
117 "net-to-net" #8: STATE_QUICK_I1: initiate
004 "net-to-net" #8: STATE_QUICK_I2: sent QI2, IPsec SA established tunnel mode {ESP/NAT=>0xb7ba4252 <0x98e5c578 xfrm=AES_256-HMAC_SHA2_256 NATOA=none NATD=192.168.22.199:4500 DPD=enabled}#在client上面ping gateway的内网和另一个client的ip,是可以ping通的
#xl2tpd配置
Road Warrior模式
# yum install xl2tpd
会安装 libpcap-1.4.0,ppp-2.4.5,xl2tpd-1.3.6 三个包
http://dl.fedoraproject.org/pub/epel/6/x86_64/epel-release-6-8.noarch.rpm #yum安装不上,先安装这玩意
设置ipsec:
# grep -v ^\# /etc/ipsec.conf|sed ‘/^$/d‘ version 2.0 # conforms to second version of ipsec.conf specification config setup # Debug-logging controls: "none" for (almost) none, "all" for lots. # klipsdebug=none # plutodebug="control parsing" # For Red Hat Enterprise Linux and Fedora, leave protostack=netkey protostack=netkey nat_traversal=yes virtual_private=%v4:192.168.0.0/16,%v4:10.0.0.0/8,%v4:172.16.0.0/12,%v4:25.0.0.0/8,%v4:!10.254.253.0/24 protostack=netkey oe=off # Enable this if you see "failed to find any available worker" # nhelpers=0 nhelpers=0 conn net-to-net authby=secret type=tunnel ike=aes256-sha2_256;modp2048 phase2alg=aes256-sha2_256;modp2048 left=192.168.22.210 leftsubnet=192.168.10.1/24 right=192.168.22.199 rightsubnet=192.168.20.1/24 forceencaps=yes dpddelay=1 dpdtimeout=3 dpdaction=restart auto=start conn l2tp-psk authby=secret pfs=no auto=add rekey=no type=transport left=192.168.22.210 leftprotoport=17/1701 right=%any rightprotoport=17/%any rightsubnet=vhost:%priv,%no
配置xl2tpd
# grep -v ^\; /etc/xl2tpd/xl2tpd.conf|sed ‘/^$/d‘ [global] listen-addr = 192.168.22.210 auth file = /etc/ppp/chap-secrets [lns default] ip range = 192.168.10.128-192.168.10.254 local ip = 192.168.10.1 require chap = yes refuse pap = yes require authentication = yes name = LinuxVPNserver ppp debug = yes pppoptfile = /etc/ppp/options.xl2tpd length bit = yes
# grep -v ^\# /etc/ppp/options.xl2tpd|sed ‘/^$/d‘ ipcp-accept-local ipcp-accept-remote ms-dns 114.114.114.114 noccp auth crtscts idle 1800 mtu 1410 mru 1410 nodefaultroute debug lock proxyarp connect-delay 5000 logfile /var/log/xl2tpd.log
# cat /etc/ppp/chap-secrets # Secrets for authentication using CHAP # client server secret IP addresses vpn * vpn 192.168.10.22 #用户名为vpn,密码为vpn,分配的ip地址为192.168.10.22
#在xp系统验证
网上邻居--创建一个新的连接--vpn--输入gateway的ip--创建完毕后,右键--属性--安全,把"要求数据加密(没有就断开)"去掉,要不会出现错误 741
点击“IPSec设置”--“使用与共享的密钥作身份验证”输入上面的密钥“test”,就可以连接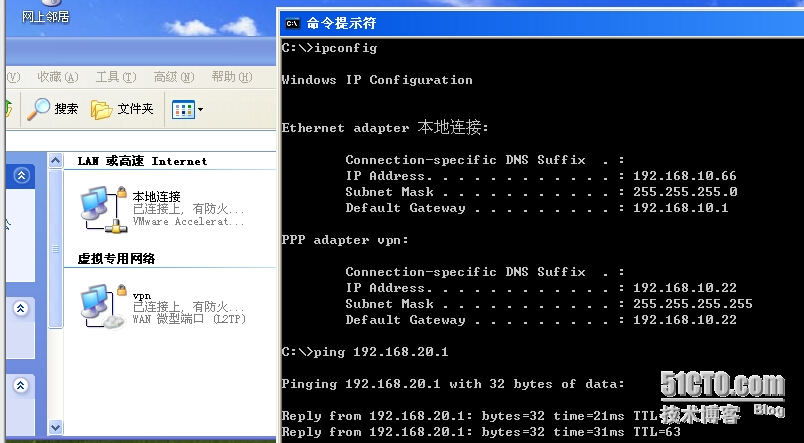
# tail /var/log/xl2tpd.log #查看日志 rcvd [IPCP ConfReq id=0x6 <addr 0.0.0.0> <ms-dns1 0.0.0.0> <ms-dns2 0.0.0.0>] sent [IPCP ConfNak id=0x6 <addr 192.168.10.22> <ms-dns1 114.114.114.114> <ms-dns2 114.114.114.114>] rcvd [IPCP ConfAck id=0x2 <addr 192.168.10.1>] rcvd [IPCP ConfReq id=0x7 <addr 192.168.10.22> <ms-dns1 114.114.114.114> <ms-dns2 114.114.114.114>] sent [IPCP ConfAck id=0x7 <addr 192.168.10.22> <ms-dns1 114.114.114.114> <ms-dns2 114.114.114.114>] found interface eth0 for proxy arp local IP address 192.168.10.1 remote IP address 192.168.10.22 Script /etc/ppp/ip-up started (pid 7472) Script /etc/ppp/ip-up finished (pid 7472), status = 0x0
参考网站:
http://www.freeswan.org/
https://github.com/xelerance/Openswan/wiki/L2tp-ipsec-configuration-using-openswan-and-xl2tpd
http://segmentfault.com/blog/tyheist/1190000000646294
http://www.360doc.com/content/09/1105/16/25127_8448328.shtml
本文出自 “金戈铁马行飞燕” 博客,请务必保留此出处http://bbotte.blog.51cto.com/6205307/1617208
郑重声明:本站内容如果来自互联网及其他传播媒体,其版权均属原媒体及文章作者所有。转载目的在于传递更多信息及用于网络分享,并不代表本站赞同其观点和对其真实性负责,也不构成任何其他建议。





































